Blog Layout
Data Dishonor: 2021’s Biggest Data Breaches & Easy Ways To Protect Yourself
October 13, 2021
Leaked Records Number In the Billions So Far In 2021
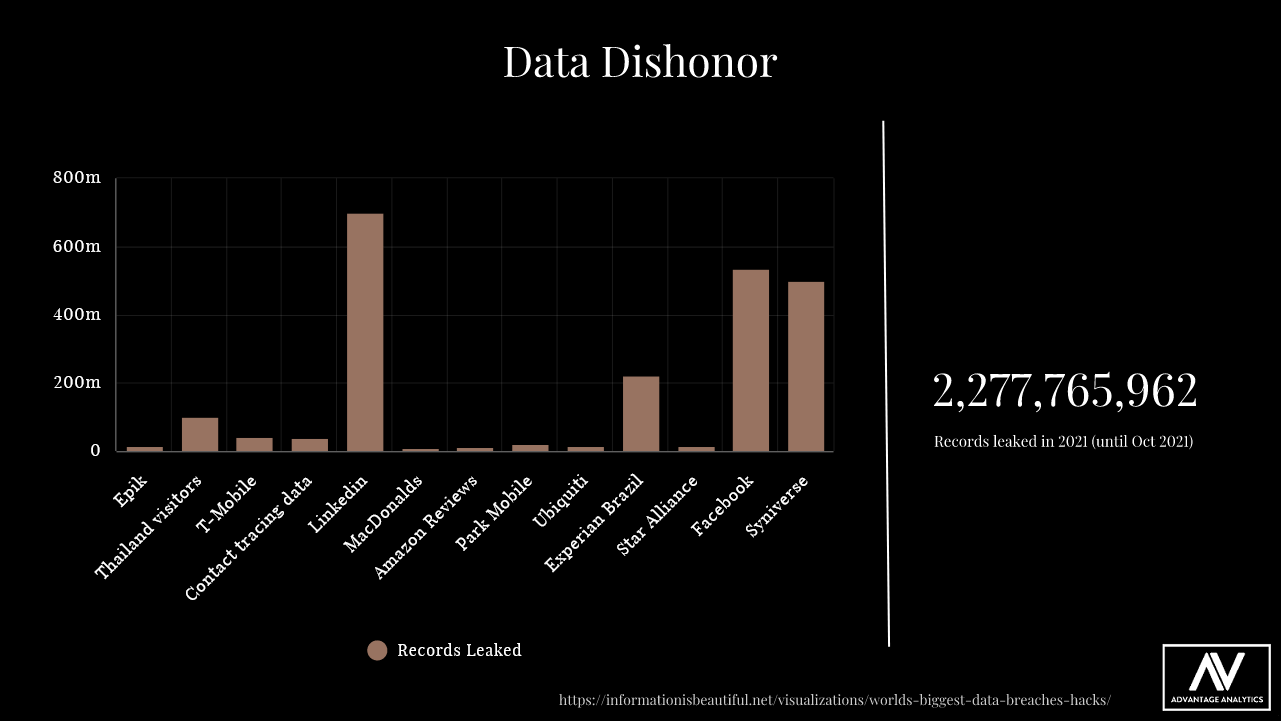
Data harvesting is now comparable to drilling for oil. Data is a valuable resource that is extracted, transformed, and profited from; so is oil. That is no wonder why 2021 has seen some of the largest increases in data theft in recent memory. 2021 is marked by being the year of the largest number of records leaked in history. We have seen billions upon billions of data records, potentially containing sensitive personal information such as address’s, birthdays, social insurance numbers, and credit card details, being infringed upon by nefarious characters. Numbers like these are staggering especially when considering that everyday people put full trust in companies that they give data to. This trust is often betrayed, betrayed by the very companies that falsely promise to safeguard our data.
The disturbing trend displayed in 2021’s data breaches is the number of leaks originating from the world’s largest organisations. Multi-national corporations like Facebook, LinkedIn, and Amazon have fallen victim to data scams. What compounds these issues is the magnitude of people who use services as these on a regular basis. As a result, there are many precautions that everyday people must put in place to protect themselves from any sort of harm that may come from a future data leak.
1. No-onsite storage
· Your data will be stored on the cloud. Most data breaches occur due to a lack of security on local IT infrastructure. Accordingly, we eliminate this possibility.
· AWS is known to be the most secure and robust storage platform there is. They employ the world’s greatest engineers and cybersecurity professionals in the industry. We trust them to do the heavy lifting.
· We discard personal metadata that makes your data unique. That way, it flows in as another part of a larger whole.
· We exclusively employ the most secure technology to communicate and process your data. Rest assured with the wonders of cryptography.
Protecting Yourself
By subtly altering to your personal devices and user accounts, you can maintain strong security against external attempts by unwanted people to access your data. In addition, many small changes can protect your privacy from other who you wouldn’t like to share your information with. Here are some general tips to protect yourself and your information online.
Strong passwords
Strong passwords are one of the first most critical line of defense against hackers. When attempting to access your accounts online, many hackers will use brute force or other techniques to try and guess what your personal credentials are. If you use common passwords like “abcdefg” to unlock your account, you are at risk. You are only making life easier for these hackers and nefarious individuals. It is imperative to use a unique phrase for each site that you log into. Hackers often break into one account and then try the same credentials on other websites too.
When creating a brand-new password, you’ll need to include a complex mix of characters, which include numbers, letters, and symbols. Things like uppercase and lowercase words, numbers and symbols and lengthy phrasing are what you should aim for. The length of your passwords is personal preference, but 10 characters is a sufficient length. It’s also important that you probably shouldn’t use full words that can be found dictionaries, as hackers have common password databases that may contain many common words.
The best way to go create passwords is to condense a longer sentence into a complex set of character. Something like “Margret Thatcher is 100% sexy” is easy to remember. That is important because it can easily be abridged to “MrgrtThtchris110%SEXY.” This password is long, complex, and there is very little chance that a hacker would be able to quickly guess it. Tricks like these can go a very long way in protecting your accounts.
HTTPS utilization
The man-in-the-middle attack is a very common hacking technique. This method is when hackers find ways to listen in on the data that you’re transferring over the internet. If you like to shop online, this can become a huge problem, as this gives outsiders the ability to copy your credit card information when you check out.
Fortunately, cybersecurity experts have come up with a solution: HTTPS encryption. HTTPS technology scrambles any information that is sent to a company that utilizes HTTPS, thereby making it practically infeasible for hackers to see what data is being transmitted. Even more, is that it is incredibly easy to see if a site uses HTTPS. Looking at the URL bar will show a small green lock on encrypted website. This can give you the assurance that your connection is secured.
Don’t fall for phishing attacks
One of the most effective hacking tools is phishing. It is essentially going through the path of least resistance to get your valuable information. A phishing campaign is when a hacker, disguised as someone else, simply asks victims to either provide sensitive information, or even getting people to click a malicious link. This involves the hacker disguising themselves as a trustworthy character, such as a lottery corporation or a government organization. These individuals can go far lengths to legitimize their operation. Often some hackers use images of the company logos and professional pictures to deceive people.
What’s more is that many hackers have also began mixing ransomware into their phishing attacks. Ransomware is a specific malware variant that’s purpose is to encrypt your data. This essentially locks you out of your files until you pay the attacked to unlock your files. The last thing that you want to do is have to pay to get access to your files, along with having your information compromised.
Staying alert is some of the main ways you can prevent phishing. For example: Always double-check the sender’s address to make sure it is from a known source, never click random links in emails from strangers, and finally, the prince of a foreign country doesn’t really have millions in a foreign bank account that they want to share with you. Ultimately, you must use common sense, and always heed to the parable: If it is too good to be true, it probably isn’t.
Although there are many ways you can avoid being hacked, what is of paramount importance is that you need to remain vigilant. Paying attention to your online activity is like driving. Everyone knows the rules, and many follow them. But there are always the few bad apples you must watch out for. Be careful and you can protect yourself, eventually it could save you a major headache down the road.
Share
Tweet
Share
Mail
June 7, 2021
Data generation is essential to any business function. Data is something that modern organizations cannot do without. Competing in an internet connected world now requires the use of analytics to supplement traditional decision making frameworks. The article below highlights how text analysis can be used to locate and extract info from big data. We at Advantage Analytics incorporate text analysis in our analytical framework to give our clients results that give them an edge over the competition. Contact us now for more info. Link to Article: http://ijece.iaescore.com/index.php/IJECE/article/view/10540
Free Evaluation
We are the experts in data. Our consulting advice is based on years of training, hard work, and passion, as well as familiarity with data analytics, statistics and AI. You’ll find all that and more at Advantage Analytics.
Thank you for contacting us.
We will get back to you as soon as possible
We will get back to you as soon as possible
Oops, there was an error sending your message.
Please try again later
Please try again later
About Us
Powering data-driven insights for a wide variety of industries. Trust us to help you gain an edge in the digital world.
Contact info
230-997 Seymour Street, Vancouver, BC, Canada V6B 3M1
604-902-4325
info@advantageanalyticsgroup.com




